As technology evolves, ensuring the integrity and confidentiality of sensitive information becomes an essential part of digital interactions. This is where SSH keys, a cornerstone of modern cybersecurity, come into play. The ability to securely authenticate and establish encrypted connections between systems is at the heart of SSH key technology.
In this comprehensive guide, we will delve into the intricate process of generating and effectively utilizing SSH keys specifically tailored for Ubuntu, one of the most widely adopted and user-friendly Linux distributions.
Through step-by-step instructions, insights into key management best practices, and a deeper understanding of the underlying cryptographic principles, both novice users and seasoned professionals will gain a firm grasp of how SSH keys can fortify their digital interactions.
What Is A Public Key Authentication?
This method eliminates the need for sharing sensitive information like passwords across the network, enhancing security and reducing the risk of unauthorized access:
- Public Key: The public key is, as the name suggests, publicly available and can be freely distributed. It is used to encrypt data that is intended to be sent securely to the owner of the corresponding private key;
- Private Key: The private key is kept secret and is known only to the owner. It is used to decrypt data that has been encrypted using the corresponding public key;
The Process of Public Key Authentication
Public key authentication operates on a simple yet powerful principle: data encrypted with one key can only be decrypted with the other key in the pair.
The authentication process typically unfolds as follows:
- Key Generation: A user or entity generates a pair of keys: the public key and the private key. These keys are mathematically linked but computationally infeasible to deduce one from the other;
- Distribution of Public Key: The public key is shared openly and can be stored on servers, sent in emails, or even printed on business cards. Its exposure does not compromise security since it is used for encryption, not decryption;
- Authentication Request: When a user attempts to access a system (such as a remote server), the system requests proof of identity;
- Challenge Encryption: The system generates a random challenge and encrypts it with the user’s public key;
- Decryption with Private Key: The user receives the encrypted challenge and decrypts it using their private key. This action proves they possess the corresponding private key, thus establishing their identity;
- Response Submission: The decrypted challenge is sent back to the system;
- Authentication Verification: The system decrypts the response using the stored public key. If the decrypted challenge matches the original challenge, the user is authenticated;
Advantages of Public Key Authentication
Public key authentication offers several compelling advantages over traditional authentication methods:
- Enhanced Security: Public key authentication eliminates the need to transmit sensitive information over the network, reducing the risk of interception and unauthorized access;
- No Passwords: Users are not required to remember and manage passwords, which can be challenging and potentially insecure;
- Key-Based Access Control: Public key authentication enables granular access control. Users can be granted access to specific resources based on their keys;
- Non-Repudiation: Public key authentication provides a strong basis for non-repudiation. A user cannot deny their actions if their private key was used to authenticate
- Scalability: As public keys can be easily distributed, public key authentication scales well, even in large and complex systems [2];
Applications of Public Key Authentication
Public key authentication finds widespread use across various domains, including:
- SSH Authentication: Secure Shell (SSH) uses public key authentication to enable secure remote access to servers. Administrators can securely manage servers without exposing passwords to potential attackers;
- Secure Data Transfer: Public key authentication is integral to secure data transfer protocols like SFTP (Secure File Transfer Protocol) and HTTPS. It ensures the confidentiality and integrity of transmitted data;
- Digital Signatures: Public key authentication forms the foundation of digital signatures, which verify the authenticity and integrity of electronic documents and transactions;
- Virtual Private Networks (VPNs): Public key authentication enhances the security of VPN connections, ensuring that only authorized users can access the network;
- Email Encryption: Public key authentication enables encrypted email communication, ensuring that only the intended recipient can read the contents of the message;
Best Practices for Public Key Authentication
To ensure the effectiveness and security of public key authentication, it’s important to follow the best practices:
- Keep Private Keys Secure: Private keys should be stored in a secure location, protected by strong encryption and access controls;
- Regular Key Rotation: Periodically rotate keys to mitigate the risk of long-term key compromise;
- Use Passphrases: When generating private keys, use strong passphrases to add an extra layer of security;
- Audit and Monitoring: Regularly audit and monitor key usage to detect any suspicious or unauthorized activities
- Key Revocation: In case of key compromise, ensure a mechanism for revoking and replacing keys exists;
What Are SSH Keys?
SSH keys, short for Secure Shell keys, are a pair of cryptographic keys used to establish secure and encrypted communication between a client (your computer) and a server (remote computer). SSH keys provide a more secure and convenient way to authenticate and connect to remote servers or services compared to traditional password-based authentication [3].
SSH keys consist of two components: a public key and a private key. These keys are created using advanced encryption algorithms and work together to enable secure communication:
- Public Key: The public key is meant to be shared openly and can be freely distributed. It is used to encrypt data that is sent to the server. While it’s called a “public” key, sharing it does not compromise security. The public key is stored on the server you want to connect to, allowing the server to encrypt data that only the corresponding private key can decrypt;
- Private Key: The private key is kept secret and known only to the owner. It is used to decrypt data that has been encrypted with the corresponding public key. The private key must be safeguarded and should never be shared or exposed to others. If someone gains access to your private key, they could potentially impersonate you and gain unauthorized access to systems that you have access to;
When you attempt to connect to a remote server using SSH, the following process takes place:
- The server sends a unique challenge to the client;
- The client uses its private key to encrypt the challenge;
- The server decrypts the challenge using the corresponding public key stored on the server;
- If the decrypted challenge matches the original challenge, the client is authenticated and granted access;
SSH keys offer several advantages over password-based authentication:
- Enhanced Security: SSH keys are much harder to guess or crack than passwords;
- No Passwords: You don’t need to remember or transmit passwords, reducing the risk of exposure;
- Automation: SSH keys are often used for automated tasks or scripts that need to connect to remote servers without user interaction;
- Key-Based Access Control: Administrators can control access by managing the authorized public keys on the server;
- Non-Repudiation: SSH key usage provides a basis for non-repudiation. If your private key was used, you cannot deny your actions;
To use SSH keys, you need to generate a key pair on your local machine, add the public key to the remote server’s ~/.ssh/authorized_keys file, and then use your private key to authenticate when connecting. This process ensures a secure and efficient means of communication and access to remote systems.
What Is Ubuntu?
Ubuntu is a widely used and popular open-source operating system based on the Debian distribution of Linux. It is known for its user-friendly interface, strong community support, and emphasis on ease of use and accessibility. Ubuntu is designed to be versatile and can be used for various purposes, including desktop computing, servers, cloud computing, and development [4].
Key features and characteristics of Ubuntu include:
- Open Source: Ubuntu is built on open-source software, which means its source code is freely available for anyone to view, modify, and distribute;
- Linux Kernel: Ubuntu uses the Linux kernel as its core component. The Linux kernel is responsible for managing hardware resources, providing a foundation for running applications and services;
- Desktop Environment: Ubuntu offers a range of desktop environments, including the default GNOME desktop environment, as well as variants like Ubuntu KDE, Xfce, and more. These environments provide the graphical user interface and tools that users interact with;
- Software Package Management: Ubuntu uses the APT (Advanced Package Tool) package management system to install, update, and manage software packages. The Ubuntu Software Center or the command-line interface can be used to search for and install software;
- Software Repository: Ubuntu maintains an extensive repository of software packages that users can easily access and install. This repository contains a wide range of applications, utilities, and tools for various purposes;
- Regular Releases: Ubuntu follows a predictable release schedule, with new versions released every six months (April and October). Each version is supported for a specific period, typically 9 months for standard releases and 5 years for Long-Term Support (LTS) releases;
- LTS Releases: LTS releases are intended for long-term use and come with extended support. They are well-suited for production servers, enterprise environments, and systems that require stability and security updates over an extended period;
- Server Edition: Ubuntu Server is a variant of Ubuntu optimized for server environments. It includes features and tools for managing and deploying servers, virtualization, containerization, and cloud computing;
- Cloud and Containers: Ubuntu is widely used in cloud computing platforms and is a popular choice for creating and managing virtual machines and containers due to its lightweight nature and strong support for cloud technologies;
- Community and Support: Ubuntu has a large and active community of users and developers. Online forums, documentation, and community-driven resources make it easy to find help, troubleshoot issues, and collaborate with others;
- Security: Ubuntu emphasizes security and regularly releases updates and patches to address vulnerabilities and enhance system security;
Whether you’re a casual desktop user, a developer, or a system administrator, Ubuntu offers a versatile and powerful platform that can be customized and tailored to your specific needs. Its user-friendly interface, robust software ecosystem, and strong community support make it a popular choice for individuals and organizations looking for a reliable and open-source operating system.
Why Does Ubuntu Need SSH Keys?
Ubuntu, like any other operating system, doesn’t inherently “need” SSH keys. However, SSH keys are commonly used with Ubuntu (or any Linux-based system) for various reasons related to security, authentication, and ease of use, especially in scenarios involving remote access and communication.
Here are some of the key reasons why Ubuntu (or any Linux system) might use SSH keys:
- Secure Remote Access: SSH keys provide a more secure way to access remote systems compared to traditional password-based authentication. Passwords can be guessed, cracked, or intercepted, while SSH keys use strong cryptographic algorithms to establish secure connections;
- Authentication: SSH keys serve as a means of authentication. When a user tries to log in to a remote server, their SSH key is used to verify their identity, reducing the reliance on passwords;
- Strong Encryption: SSH keys use strong encryption techniques to secure communication between the client and server. This ensures that data transmitted between the two remains confidential and cannot be easily intercepted;
- Automation: SSH keys are often used for automated tasks, scripting, and system administration. They allow programs and scripts to establish secure connections without requiring manual intervention to enter passwords;
- Key-Based Access Control: System administrators can control who has access to a server by managing the authorized public keys. Users without a valid SSH key won’t be able to access the server, enhancing access control;
- Non-Repudiation: SSH key usage provides a basis for non-repudiation. If a private key is used to authenticate, the user cannot later deny their actions;
- Passwordless Login: With SSH keys, users can log in to remote servers without needing to remember or enter passwords, making the login process faster and more convenient;
- Secure File Transfers: SSH keys are commonly used to secure file transfers using protocols like SCP (Secure Copy Protocol) or SFTP (Secure File Transfer Protocol);
- Server Management: SSH keys are crucial for server management and remote administration. They allow administrators to securely access servers and perform maintenance tasks;
- Cloud Services: When using cloud services or virtual private servers (VPS), SSH keys are often the recommended way to access and manage the instances. Many cloud providers encourage or require the use of SSH keys for enhanced security;
- Multi-Factor Authentication (MFA): SSH keys can be used as part of a multi-factor authentication strategy, adding an additional layer of security on top of the key-based authentication [5];
It’s important to note that while SSH keys offer significant security benefits, they also require careful management. The private key must be kept secure and should never be shared or exposed. Regular maintenance, key rotation, and monitoring are essential to maintaining the security of SSH key-based authentication.
The Benefits of Using SSH Keys Over Passwords
Using SSH keys over passwords offers numerous benefits that enhance security, streamline authentication, and improve overall user experience.
Here are the key advantages of using SSH keys:
Enhanced Security
SSH keys use strong cryptographic algorithms, making them highly secure against unauthorized access, brute-force attacks, and eavesdropping. Unlike passwords, which can be guessed or cracked, SSH keys provide a higher level of protection for sensitive systems.
Elimination of Passwords
SSH keys eliminate the need for passwords altogether, reducing the risk associated with password-related vulnerabilities such as weak passwords, password reuse, and phishing attacks.
Resistance to Sniffing and Interception
Passwords sent over the network can be intercepted by malicious actors. SSH keys prevent this risk because the private key remains on the local machine, and only the public key is sent to the server.
Key-Based Authentication
SSH keys provide a key-based authentication mechanism, offering a more secure and convenient way to verify a user’s identity. This is especially useful in environments where strong security is crucial.
Automation and Scripting
SSH keys enable the automation of tasks and scripting, as programs and scripts can use keys to establish secure connections without manual intervention, streamlining processes and improving efficiency.
Key-Based Access Control
Administrators can control access to systems by managing authorized public keys. Users without a valid SSH key won’t be able to access the system, improving access control.
Non-Repudiation
SSH key usage provides a basis for non-repudiation. If a private key is used to authenticate, the user cannot later deny their actions.
Convenience and Efficiency
SSH keys offer passwordless logins, eliminating the need to remember or type passwords. This results in a faster and more seamless authentication process.
Secure Remote Access
SSH keys are a trusted method for secure remote access to servers, ensuring that only authorized users can log in and manage systems.
Secure File Transfers
SSH keys are commonly used to secure file transfers using protocols like SCP (Secure Copy Protocol) or SFTP (Secure File Transfer Protocol), safeguarding data during transit.
Multi-Factor Authentication (MFA)
SSH keys can be used in combination with other authentication methods, such as passwords or biometrics, to create a multi-factor authentication setup for added security layers.
No Shared Secrets
Unlike passwords, SSH keys do not involve any shared secrets that need to be exchanged between the user and the server, reducing the risk of exposure.
Centralized Key Management
Organizations can centrally manage and distribute SSH keys, making it easier to grant and revoke access across a large number of systems.
Long-Term Support
SSH keys have been a proven and trusted authentication method for decades, ensuring long-term compatibility and support [6].
Adding Your Public Key to a Remote Server:
Add Public Key Via CLI
The command-line interface provides a direct and efficient way to add your public key to a remote server.
Here’s a step-by-step process:
Generate Your SSH Key Pair: If you haven’t already, generate your SSH key pair using the ssh-keygen command on your local machine. This command generates your public and private keys.
Copy Your Public Key: Use the cat command to display your public key in the terminal:
cat ~/.ssh/id_rsa.pub
Copy the entire output.
Connect to the Remote Server: Open a terminal and use the ssh command to connect to the remote server:
ssh username@remote_server_ip
Replace the username with your remote server username and remote_server_ip with the server’s IP address.
Add the Public Key: Once connected to the server, append the copied public key to the ~/.ssh/authorized_keys file:
echo “PASTE_YOUR_PUBLIC_KEY_HERE” >> ~/.ssh/authorized_keys
Make sure to replace “PASTE_YOUR_PUBLIC_KEY_HERE” with the actual key you copied earlier.
Set Permissions: Secure the permissions of the ~/.ssh directory and the authorized_keys file:
chmod 700 ~/.ssh
chmod 600 ~/.ssh/authorized_keys
Exit the Server: After adding the key, exit the remote server [7]:
exit
Add Public Key Via FileZilla
FileZilla is a popular FTP client that also supports SSH key authentication. Here’s how to add your public key using FileZilla:
- Generate Your SSH Key Pair: Similar to the CLI method, start by generating your SSH key pair using ssh-keygen;
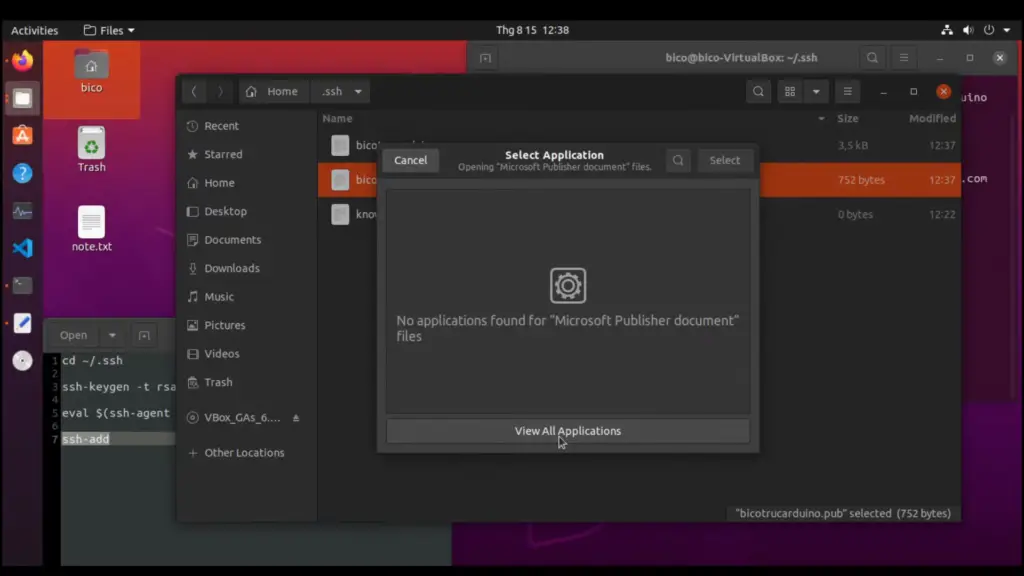
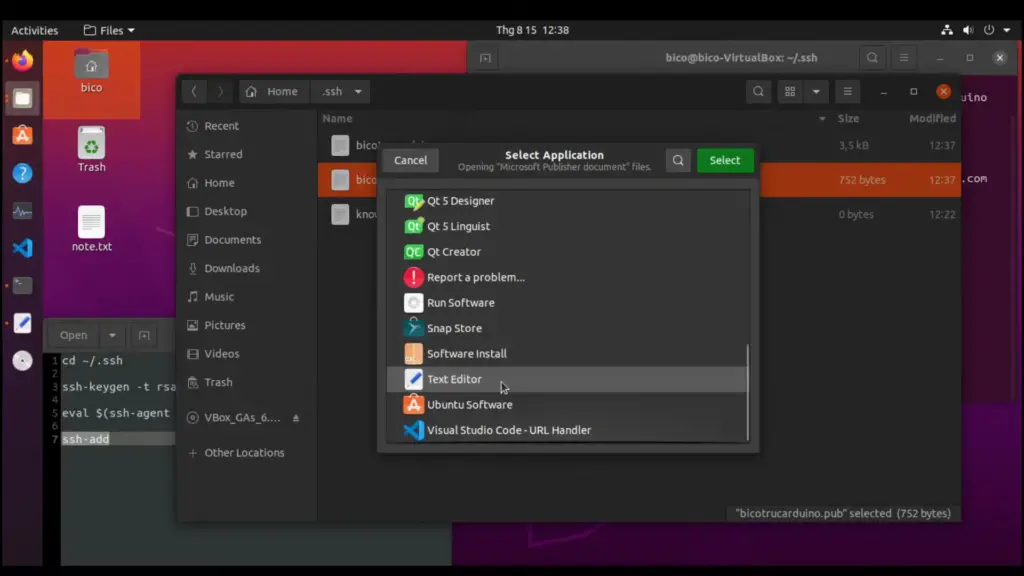
- Copy Your Public Key: Open the public key file (usually ~/.ssh/id_rsa.pub) using a text editor, and copy the entire content;
- Open FileZilla: Launch FileZilla and go to “Edit” > “Settings”;
- Navigate to SFTP: In the “Settings” window, navigate to “Connection” > “SFTP” > “Add key file”;
- Add Public Key: Click on “Add key file”, and then navigate to and select your public key file (id_rsa.pub)
- Save Settings: Click “OK” to save your settings;
- Connect to the Server: In the FileZilla main window, enter the server’s hostname, your username, and leave the password field blank;
- Connect Securely: Click “Quickconnect” and FileZilla will use your SSH key to establish a secure connection to the remote server;
How to Generate and Use SSH Keys on Ubuntu:
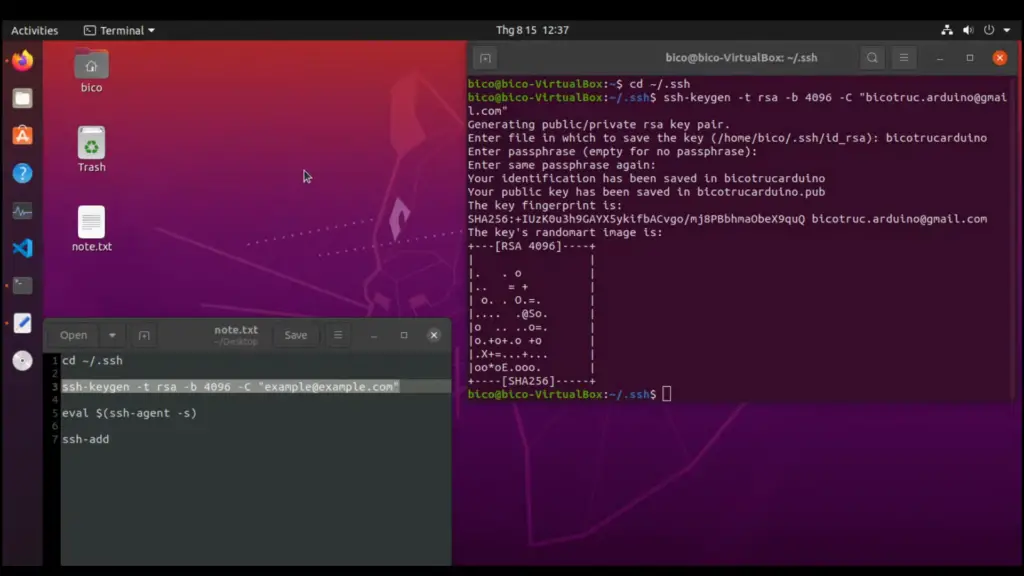
1. Creating the Key Pair
Types of Keys
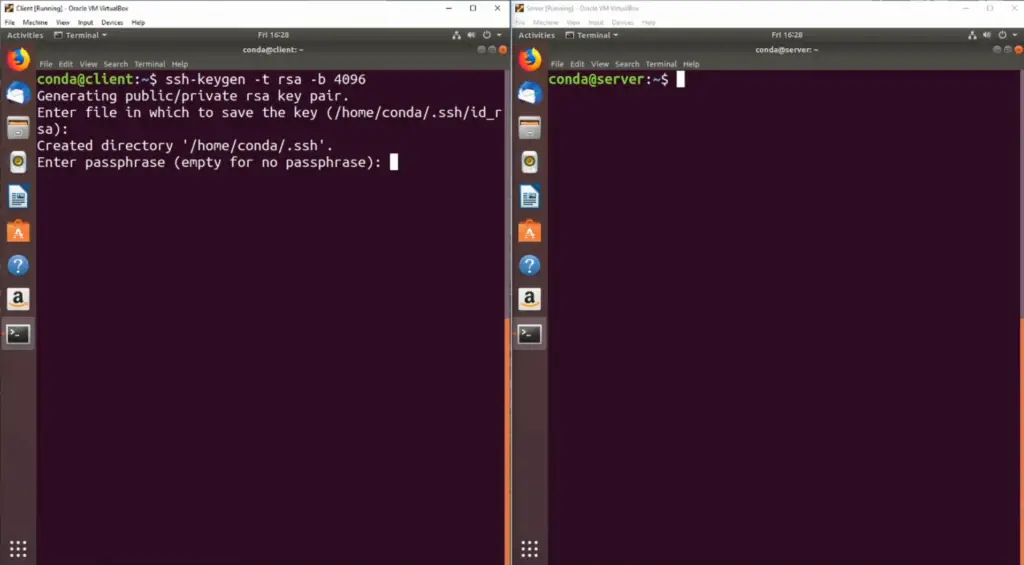
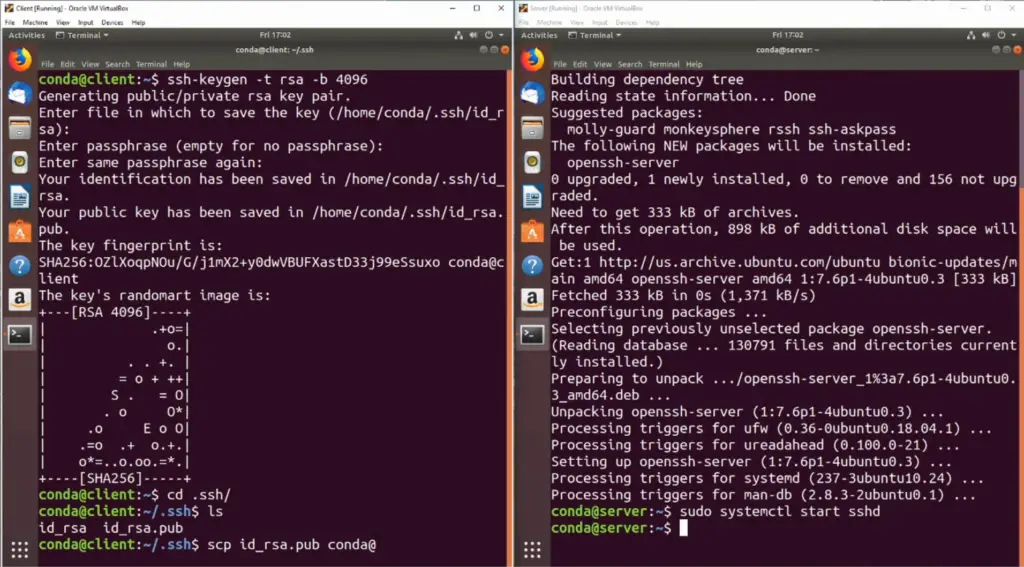
SSH keys come in various types, but the most commonly used ones are RSA and DSA. To generate a key pair, open a terminal and enter the following command:
ssh-keygen -t rsa
You can replace rsa with dsa or another type if needed.
Adding a Passphrase
To add a passphrase, run:
ssh-keygen -t rsa -b 4096 -C “your_email@example.com”
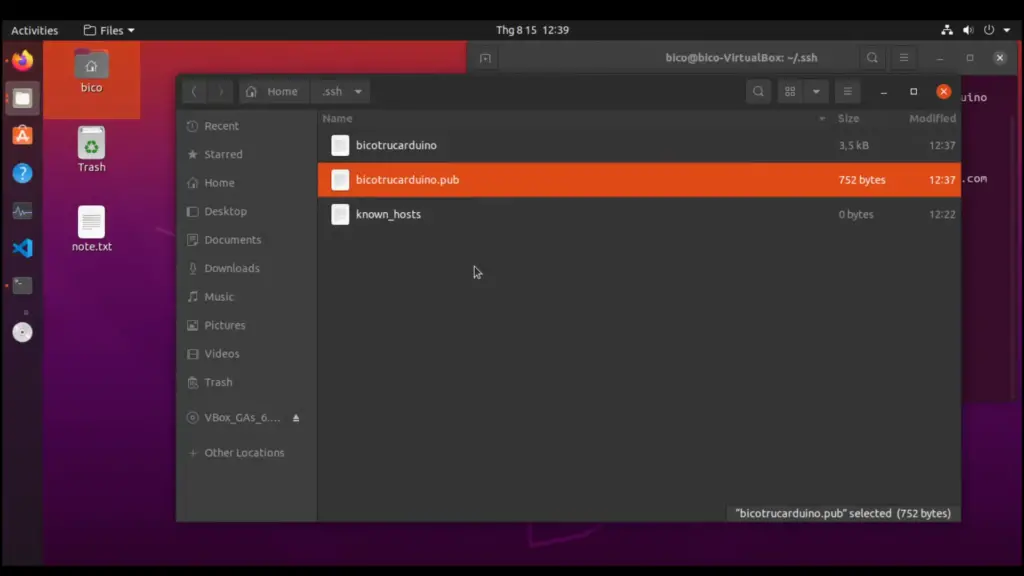
Saving Keys
The generated keys are stored by default in the ~/.ssh/ directory with filenames id_rsa (private key) and id_rsa.pub (public key). It’s important to keep your private key secure and never share it.
2. Copying the Public Key to Your Ubuntu Server
Copying the Public Key Using ssh-copy-id
To copy your public key to the remote server, you can use the ssh-copy-id command. Replace username and server_ip with your server’s credentials:
ssh-copy-id username@server_ip
This command copies your public key to the ~/.ssh/authorized_keys file on the server.
Copying the Public Key Using SSH
If ssh-copy-id is not available, you can manually copy the public key using SSH. Run this command, replacing username and server_ip:
cat ~/.ssh/id_rsa.pub | ssh username@server_ip “mkdir -p ~/.ssh && cat >> ~/.ssh/authorized_keys”
Copying the Public Key Manually
If neither of the above methods works, you can copy the contents of the id_rsa.pub file manually and add them to the remote server’s authorized_keys file:
cat ~/.ssh/id_rsa.pub
Copy the output, then log in to your server and open the ~/.ssh/authorized_keys file:
nano ~/.ssh/authorized_keys
Paste the copied key, save the file, and exit the text editor [8].
3. Authenticating Your Ubuntu Server Using SSH Keys
Now that your public key is on the server, you can authenticate without a password:
ssh username@server_ip
4. Disabling Password Authentication on Your Server
For added security, it’s recommended to disable password authentication and only allow SSH key authentication. Open the SSH configuration file on your server:
sudo nano /etc/ssh/sshd_config
Find the line that says PasswordAuthentication and change its value to no. Then, restart the SSH service:
sudo service ssh restart
This step ensures that only SSH key authentication is allowed, further strengthening your server’s security.
FAQ:
1. How to add or replace a passphrase for an existing private key?
To add or replace a passphrase for an existing private key, you can use the ssh-keygen command with the -p option. Open a terminal and enter:
ssh-keygen -p
You will be prompted to enter the path to the private key and then to provide the new passphrase.
2. How to back up an existing private/public key?
To back up an existing private/public key pair, you simply need to copy the respective key files to a secure location. For example, if your keys are stored in the ~/.ssh/ directory, you can use the cp command:
cp ~/.ssh/id_rsa ~/.ssh/id_rsa.backup
cp ~/.ssh/id_rsa.pub ~/.ssh/id_rsa.pub.backup
3. How to protect SSH keys?
To protect SSH keys, follow these measures:
- Set strong permissions on key files: Use chmod 600 ~/.ssh/id_rsa to restrict access to your private key;
- Use a passphrase: Encrypt your private key with a passphrase;
- Store keys in a secure location: Avoid sharing or storing keys in publicly accessible locations;
- Regularly update and rotate keys: Change keys periodically to reduce the risk of compromise;
- Disable password authentication: Rely solely on SSH keys for authentication;
4. How to create and set up an OpenSSH config file to create shortcuts for servers you frequently access?
To create an OpenSSH config file, open ~/.ssh/config in a text editor and add entries for each server:
Host shortcut_name
HostName server_address
User your_username
IdentityFile ~/.ssh/your_private_key
Save the file, and you can then use ssh shortcut_name to quickly connect to the server.
5. How to generate SSH keys in Ubuntu?
To generate SSH keys in Ubuntu, open a terminal and use the ssh-keygen command:
ssh-keygen -t rsa -b 4096 -C “your_email@example.com”
6. How to use a generated SSH key?
After generating an SSH key, you can use it to securely authenticate with remote servers. Copy the public key to the remote server’s ~/.ssh/authorized_keys file and use the private key for authentication from your local machine.
7. How to generate and register an SSH key?
Generate an SSH key using ssh-keygen and then register the public key on the remote server by copying it to the ~/.ssh/authorized_keys file.
8. How to add an SSH key to a new user of Ubuntu?
Copy the new user’s public key to the new user’s ~/.ssh/authorized_keys file. You may need to create the .ssh directory and set the correct permissions.
9. How to import new SSH keys from Ubuntu?
To import new SSH keys, copy the public key to the remote server’s ~/.ssh/authorized_keys file, following the same process as for generating and registering SSH keys.
10. How to get the SSH key already generated?
Your SSH keys are typically stored in the ~/.ssh/ directory. You can view your public key using:
cat ~/.ssh/id_rsa.pub
11. How to generate an SSH key in Ubuntu 22?
The process to generate an SSH key in Ubuntu 22 is the same as in previous versions. Use the ssh-keygen command to generate the keys.
12. How to connect to an SSH key?
To connect to a server using an SSH key, use the ssh command followed by the username and server address:
ssh username@server_address
13. How to log in with an SSH key in Ubuntu?
To log in with an SSH key in Ubuntu, use the ssh command followed by your username and server address. The key pair will be used for authentication.
14. How to send SSH keys to the server?
You can send your SSH public key to the server by copying the contents of ~/.ssh/id_rsa.pub and appending them to the ~/.ssh/authorized_keys file on the server.
15. How to generate SSH key Ubuntu ed25519?
To generate an SSH key using the ed25519 algorithm in Ubuntu, use the following command:
ssh-keygen -t ed25519 -C “your_email@example.com”
16. Where are the SSH keys stored in Ubuntu?
SSH keys are typically stored in the ~/.ssh/ directory on your Ubuntu machine.
17. Should you generate multiple SSH keys?
Generating multiple SSH keys is recommended if you need to access different servers or services. It provides better access control and separation of identities.
18. How to add an SSH key to a user in Linux?
To add an SSH key to a user in Linux, copy the public key to the user’s ~/.ssh/authorized_keys file.
19. How to get SSH public key Linux?
You can retrieve the SSH public key on Linux using:
cat ~/.ssh/id_rsa.pub
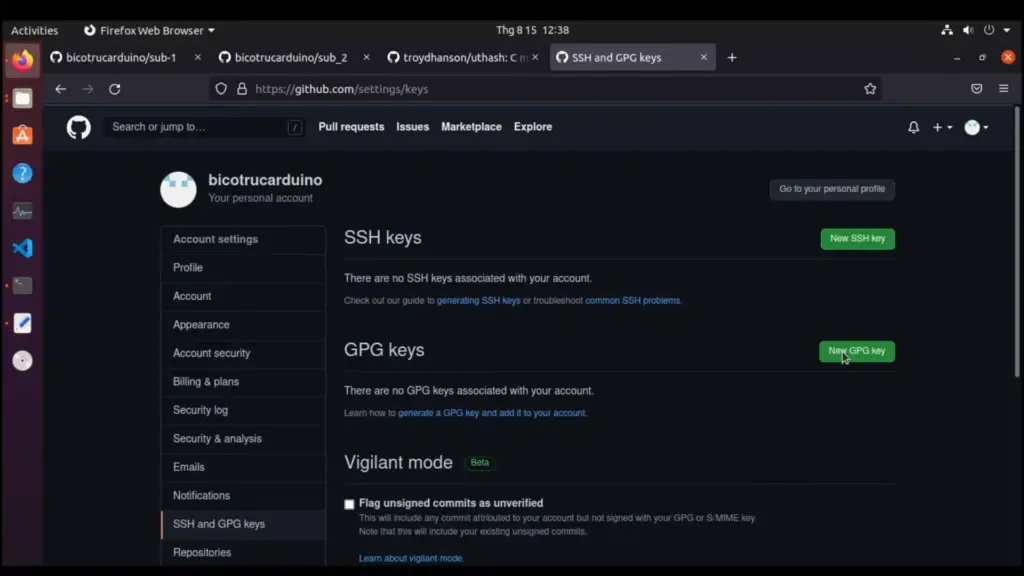
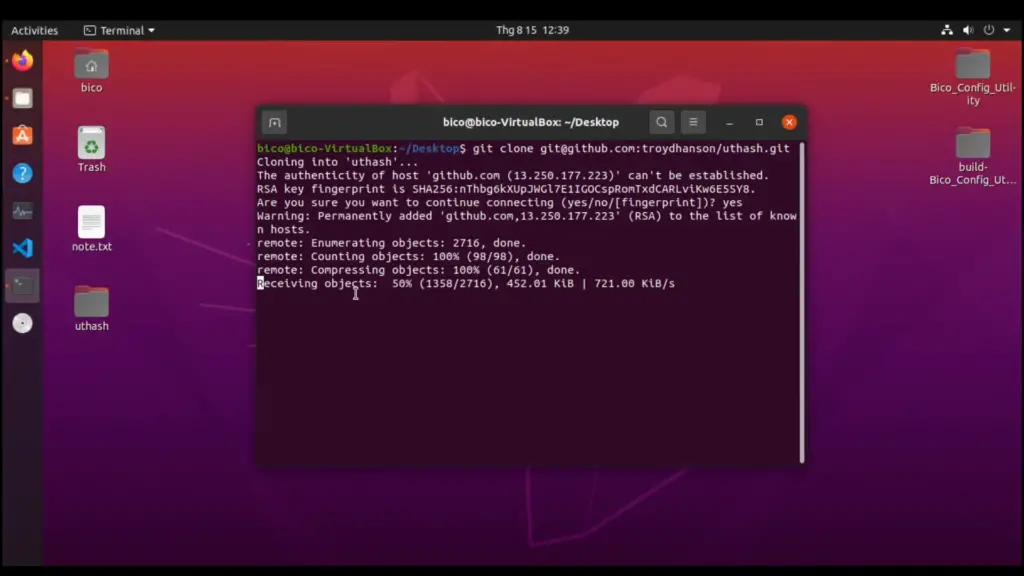
Useful Video: Creat SSH key in Ubuntu to access Github via SSH
References
- https://www.tutorialspoint.com/how-to-generate-ssh-keys-on-ubuntu
- https://www.digitalocean.com/community/tutorials/how-to-set-up-ssh-keys-on-ubuntu-20-04
- https://linuxhint.com/generate-ssh-key-ubuntu/
- https://www.cloudpanel.io/tutorial/set-up-ssh-keys-on-ubuntu-20-04/
- https://pimylifeup.com/ubuntu-generate-ssh-keys/
- https://linuxize.com/post/how-to-set-up-ssh-keys-on-ubuntu-20-04/
- https://phoenixnap.com/kb/generate-setup-ssh-key-ubuntu
- https://www.cyberciti.biz/faq/how-to-set-up-ssh-keys-on-linux-unix/



Leave a Reply