Amidst this digital landscape, the Raspberry Pi stands as a beacon of innovation and creativity, offering a gateway to a multitude of projects and possibilities.
However, the immense potential of the Raspberry Pi also warrants a proactive approach to security. This is where the Uncomplicated Firewall (UFW) emerges as a stalwart guardian, empowering users to fortify their Raspberry Pi against potential threats while maintaining control over network access.
In this comprehensive guide, we embark on a journey into the realm of cybersecurity for Raspberry Pi enthusiasts, as we unravel the intricacies of harnessing the UFW firewall. From allowing essential connections and managing firewall rules to monitoring access and enabling granular control, this tutorial equips you with the essential knowledge and tools to navigate the cybersecurity landscape with confidence.
Join us as we delve into the world of UFW, ensuring that your Raspberry Pi not only realizes its full potential but does so within a shield of digital armor, safeguarding your projects, data, and explorations.
Understanding UFW Firewall
UFW is based on iptables, which is a powerful firewall tool for Linux. However, iptables can be complex and challenging to work with directly. UFW simplifies the configuration process by offering a more user-friendly approach. It provides a framework that allows users to define policies for incoming and outgoing traffic.
By default, UFW denies all incoming connections and allows all outgoing connections. This default configuration provides a basic level of security. Users can then define specific rules to allow or deny traffic based on their requirements. For example, you can allow incoming SSH connections by allowing port 22 or blocking traffic from specific IP addresses.
UFW also offers additional features to enhance firewall configuration. It supports logging, allowing users to monitor firewall activity and analyze potential threats. UFW provides application profiles for popular services, making it easier to manage firewall rules for specific applications. It can also work with port forwarding and network address translation (NAT).
Why Use UFW on a Raspberry Pi?
UFW simplifies the process of configuring and managing firewall rules, making it more accessible for users who may not be familiar with complex firewall concepts. It provides an intuitive command-line interface for managing incoming and outgoing network traffic.
UFW is particularly well-suited for systems like the Raspberry Pi, where ease of use and simplicity are valued. With UFW, you can define rules that allow or deny traffic based on various criteria, such as IP addresses, ports, and protocols. This allows you to control which services and applications can communicate over the network, enhancing the security of your Raspberry Pi.
The Raspberry Pi, often used for educational and personal projects, may not receive the same level of security attention as larger servers or enterprise systems. However, it is still important to protect your Raspberry Pi from potential threats, especially if it is exposed to the internet or connected to other devices.
Here are some reasons why using UFW on a Raspberry Pi is a good idea:
- Access Control: UFW allows you to specify which IP addresses or ranges are allowed to connect to your Raspberry Pi. This helps prevent unauthorized access and reduces the risk of potential attacks;
- Defense Against Port Scans: Attackers often perform port scans to identify open ports on a target system. By using UFW to close unnecessary ports, you can reduce the exposure of your Raspberry Pi to such scanning attempts;
- Application Isolation: If your Raspberry Pi runs multiple services or applications, UFW can help isolate them by allowing or denying specific network traffic. This minimizes the impact of a security breach in one application on the others;
- Malicious Traffic Filtering: UFW can be configured to block incoming traffic from specific IP addresses known for malicious activities, such as brute force attacks or spamming;
- Enhanced Privacy: By controlling outgoing traffic, UFW can prevent certain applications from communicating with external servers, thus enhancing your privacy and reducing the risk of data leaks [2];
Using the UFW Firewall on the Raspberry Pi: Tutorial
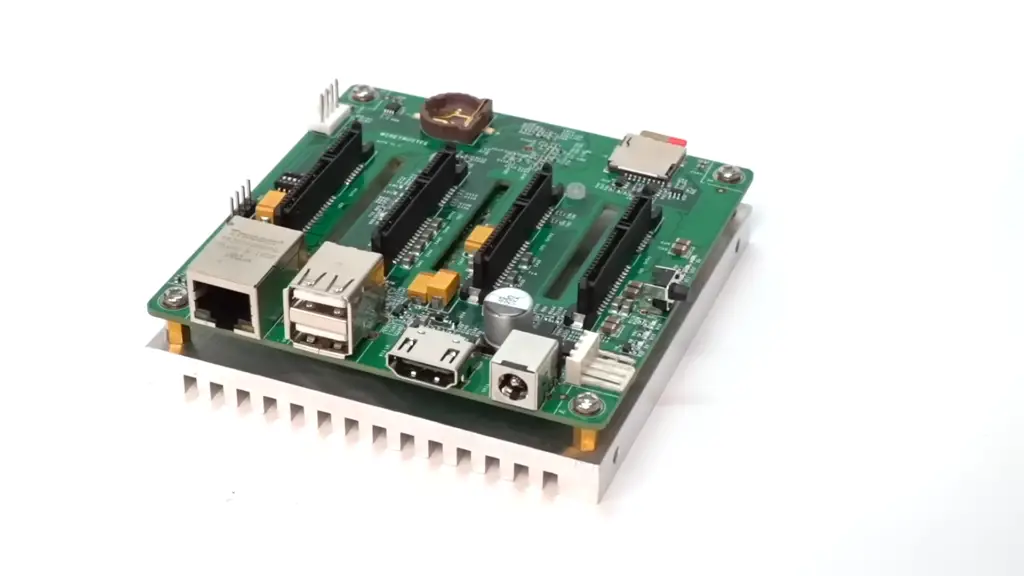
1) Necessary Equipment:
- Raspberry Pi: Choose a suitable Raspberry Pi model based on your requirements and preferences. Whether it’s the Raspberry Pi 4 with enhanced performance or an earlier version, make sure you have it at hand;
- Micro SD Card: A reliable micro SD card with sufficient storage capacity (at least 8GB) to host your Raspberry Pi’s operating system and other files;
- Ethernet Cable or Wi-Fi: Establish a network connection with either an Ethernet cable or Wi-Fi, depending on your setup;
- Power Supply: Provide a stable power supply to keep your Raspberry Pi up and running;
- Raspberry Pi Case: While not mandatory, a protective case can help shield your Raspberry Pi from dust and potential damage;
- USB Keyboard: A USB keyboard is handy for initial setup and configuration;
- USB Mouse: A USB mouse can provide additional convenience during setup and usage;
2. Installing the UFW Firewall on the Raspberry Pi
Setting up the UFW firewall on your Raspberry Pi is a crucial step in fortifying your device’s security. Follow these steps to get started.
I. Adding Firewall Rules Using UFW On the Raspberry Pi:
Allowing Access Through a Port using UFW
To allow access through a specific port using UFW, use the following command:
sudo ufw allow
Rate Limiting Connections on a Port
You can implement rate limiting for connections on a specific port with this command:
sudo ufw limit
Enabling the UFW Firewall on the Raspberry Pi
To enable the UFW firewall, use the command:
sudo ufw enable
II. Managing the UFW Service:
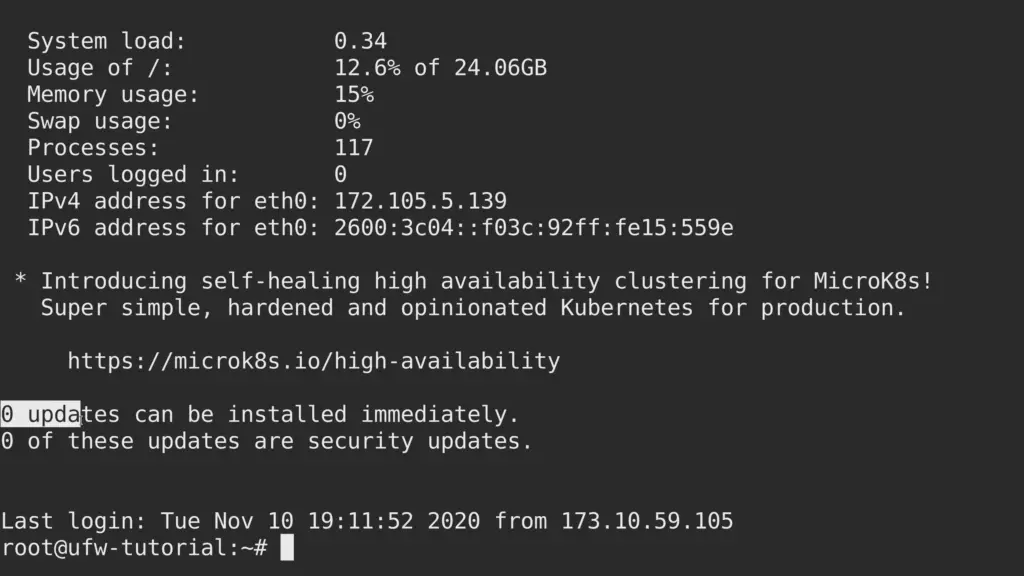
Checking UFW Firewall Status
To check the status of the UFW firewall, run:
sudo ufw status
Opening Ports in UFW to Allow Incoming Traffic
To open a specific port for incoming traffic, use:
sudo ufw allow
Implementing Connection Rate Limiting on Specific Ports
For connection rate limiting on a port, execute:
sudo ufw limit
Allowing Connections by Service Name
To allow connections by service name (e.g., SSH), use:
sudo ufw allow
Granting and Limiting Access to Trusted IP Addresses

To grant access to a specific IP address and restrict others, use:
sudo ufw allow from sudo ufw deny from
Enabling UFW Logging for Deeper Security Insights
Enabling UFW logging can provide valuable insights into security events. Use:
sudo ufw logging on
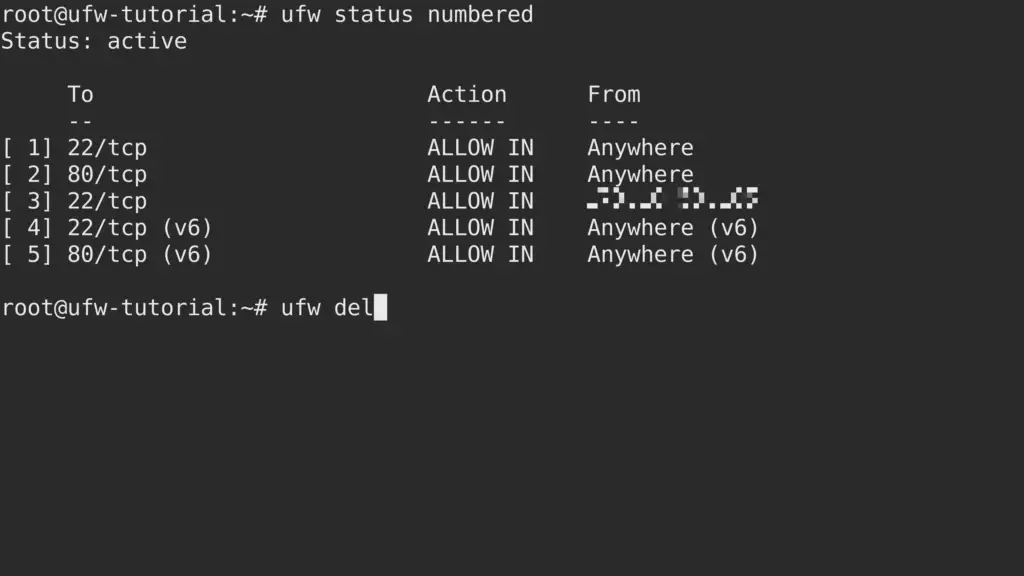
Removing Unwanted UFW Rules
To remove an unwanted UFW rule, use the delete command followed by the rule:
sudo ufw delete allow
Useful UFW Terminal Commands:
Check the UFW Firewall Status
To verify the status of the UFW firewall, simply run [3]:
sudo ufw status
Remove A Port From The Firewall List
If you want to remove a port from the firewall’s allowed list, execute:
sudo ufw delete allow
Disable The Firewall
To temporarily disable the UFW firewall, use:
sudo ufw disable
Advanced UFW Configuration
While the basic steps outlined above provide a solid foundation for securing your Raspberry Pi using UFW, there are additional configurations and considerations you might want to explore:
Logging
UFW can log denied connections and other firewall-related events. To enable logging, use:
sudo ufw logging on
Logs are stored in /var/log/ufw.log.
Application Profiles
UFW includes predefined application profiles that simplify the process of allowing specific services. You can list available profiles with:
sudo ufw app list
And then allow a specific profile, such as ‘OpenSSH’, using:
sudo ufw allow OpenSSH
Limiting Connection Rates
To prevent abuse or brute force attacks, you can limit the rate of incoming connections from a specific IP address:
sudo ufw limit from to any port
IPv6 Support
If your Raspberry Pi uses IPv6, UFW can also be configured to manage IPv6 traffic. Ensure you enable IPv6 support in the UFW configuration [4]:
sudo nano /etc/default/ufw
Change IPV6=no to IPV6=yes.

Managing Raspberry Pi Firewall Via UFW: Tips
Ensure You Allow Connections
While the primary purpose of a firewall is to block unauthorized access, you need to ensure that legitimate connections are allowed. It’s essential to strike a balance between security and usability. UFW makes this task easy. To allow connections through specific ports, use the following command:
sudo ufw allow
This command opens a specified port and permits incoming connections. For instance, if you want to enable SSH access, you’d run:
sudo ufw allow 22
Remember, allowing only necessary connections minimizes your Raspberry Pi’s exposure to potential threats.
Know How To Turn On Your Raspberry Pi Firewall
Before you can manage your Raspberry Pi firewall with UFW, you need to ensure that the firewall is turned on. To enable UFW, simply run:
sudo ufw enable
This command activates the firewall and ensures that it starts every time your Raspberry Pi boots up. Enabling the firewall is the first step toward enhancing your device’s security.
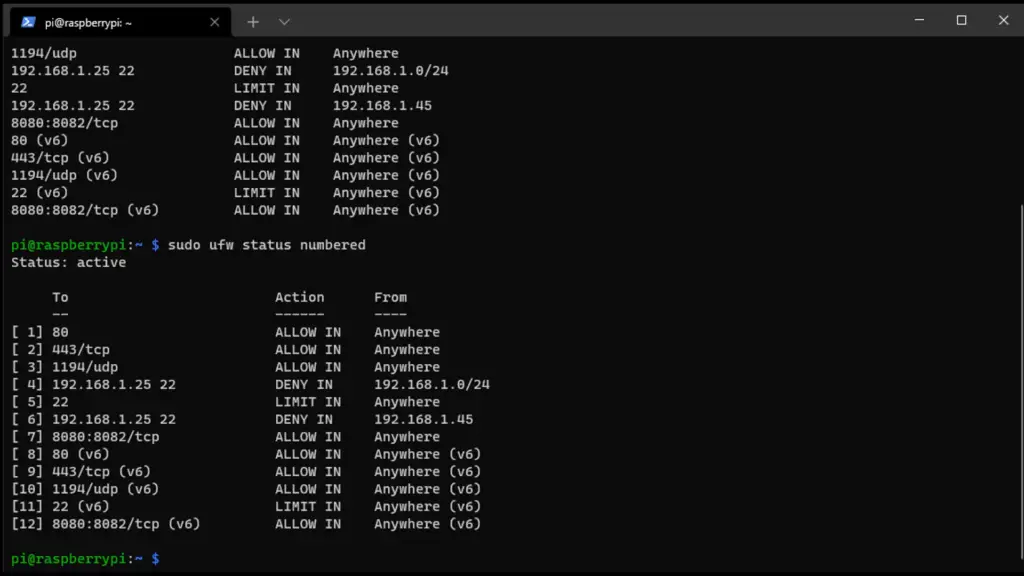
Check The Status & Rules Of The Firewall
To gain insights into the current state of your firewall and the rules that are applied, use the following command:
sudo ufw status
This command displays a summary of your firewall’s status, showing which ports are open and what type of connections are allowed. Regularly checking the status and rules help you stay informed about your Raspberry Pi’s network security.
Don’t Forget To Deny Connections
While allowing necessary connections is crucial, denying unwanted access is equally important. Denying connections from specific IP addresses or ports can further bolster your Raspberry Pi’s defense. To deny a connection, use the deny keyword followed by the IP address or port:
sudo ufw deny from
sudo ufw deny
This approach ensures that potential attackers are barred from accessing your Raspberry Pi through these entry points.
You Can Delete Existing Rules Too
As your projects and networking needs evolve, you might find it necessary to modify or remove existing firewall rules. UFW allows you to delete rules easily using the delete keyword followed by the rule you wish to remove. For example, to remove a rule that allows access to a specific port, use:
sudo ufw delete allow
Regularly reviewing and managing your firewall rules helps maintain a secure and optimized network environment.
You Can Also Disable The Firewall If You Want
There might be situations where you need to temporarily disable the firewall. Perhaps you’re troubleshooting connectivity issues or testing network configurations. To disable UFW temporarily, use:
sudo ufw disable
Remember, while disabling the firewall temporarily can be useful, always re-enable it as soon as your testing or troubleshooting is complete to maintain your Raspberry Pi’s protection [5].
UFW Best Practices
To ensure the effectiveness of UFW, it’s important to follow best practices. Regularly updating your UFW rules is crucial to stay protected against new threats. Testing your rules will help you identify any misconfigurations or conflicts. Monitoring UFW logs allows you to detect suspicious activity and take necessary action. You can also automate UFW rules using scripts for ease of management.
Troubleshooting UFW Issues
In some cases, you may encounter issues with UFW. For example, UFW may block legitimate traffic or fail to block unwanted traffic. Rule conflicts can also occur, causing unexpected behavior. To troubleshoot these issues, you can check UFW logs, review your rule configurations, and make necessary adjustments:
Check UFW Status and Rules
Start by checking the status of UFW and the rules that are currently in place. Open a terminal on your Raspberry Pi and run the following commands:
sudo ufw status
sudo ufw status verbose
This will display the current status of UFW and the rules that are being enforced.
Check Application Profiles
UFW provides application profiles that simplify rule management. Ensure that the correct application profiles are enabled. You can list available application profiles using:
sudo ufw app list
Enable a profile with
sudo ufw allow ‘Profile Name’
Check Default Policies
Make sure that the default policies are set to allow outgoing traffic and deny incoming traffic:
sudo ufw default deny incoming
sudo ufw default allow outgoing
Review Specific Rules
Examine your custom rules to ensure they’re correctly configured. For example, to allow SSH traffic:
sudo ufw allow 22/tcp
Make sure to specify the correct protocol (tcp/udp) and port number.
Check for Conflicting Rules
Sometimes, conflicting rules can cause unexpected behavior. Check for any conflicting rules that might be overriding your intended settings.
Check Logging
UFW provides logging that can help you diagnose issues. You can view UFW logs in /var/log/ufw.log:
sudo tail -f /var/log/ufw.log
This will display the UFW logs in real time.
Restart UFW
If you’ve made changes to UFW rules, it’s a good idea to restart UFW to apply the changes:
sudo ufw disable
sudo ufw enable
Check System Configuration
Ensure that your Raspberry Pi’s network configuration is correct. Check IP addresses, subnet masks, and gateway settings to ensure proper network communication.
Check Network Services
If you’re having trouble accessing specific services, make sure the services are running and configured correctly.
Check Connectivity
If you’re having trouble accessing your Raspberry Pi remotely, ensure that you have network connectivity and that the necessary ports are open.
Check Hardware Issues
If you’re still experiencing issues, consider checking your Raspberry Pi’s hardware, including networking components, cables, and power supply.
Community Resources
FAQ:
1. How do you use Raspberry Pi 4 as a firewall?
You can use a Raspberry Pi 4 as a firewall by installing and configuring firewall software like UFW (Uncomplicated Firewall). UFW allows you to manage incoming and outgoing traffic, set rules, and control access to your Raspberry Pi. By configuring UFW rules, you can filter and secure network traffic, enhancing the device’s security.
2. Does Raspberry Pi have UFW?
Yes, Raspberry Pi supports UFW (Uncomplicated Firewall), a user-friendly interface for managing iptables firewall rules. UFW simplifies firewall configuration and rule management, making it an excellent choice for securing your Raspberry Pi.
3. How to monitor home traffic on Raspberry Pi?
You can monitor home network traffic on a Raspberry Pi using tools like Wireshark or tcpdump. These tools capture and analyze network packets, providing insights into data flowing through your network.
4. Is Raspberry Pi VPN free?
While the Raspberry Pi itself is a hardware device that you need to purchase, you can set up a VPN (Virtual Private Network) on it using free and open-source software like OpenVPN. However, you might need to pay for VPN service if you choose to route your traffic through a commercial VPN provider.
5. How to deal with the port using UFW on Raspberry Pi?
You can manage ports using UFW on Raspberry Pi by allowing or denying access to specific ports. For example, to allow incoming traffic on port 80 (HTTP), you’d use: sudo ufw allow 80/tcp. To deny access, you’d replace allow with deny.
6. How to change the default policies of UFW on Raspberry Pi?
To change the default policies of UFW (e.g., to deny all incoming and allow all outgoing), you can use commands like sudo ufw default deny incoming and sudo ufw default allow outgoing.
7. How to enable IPv6 on the UFW firewall on Raspberry Pi?
To enable IPv6 on UFW, use: sudo ufw ipv6 enable.
8. How to deal with a particular IP by UFW on Raspberry Pi?
You can allow or deny access to a particular IP address using commands like sudo ufw allow from or sudo ufw deny from .
9. How to delete the rule of UFW on Raspberry Pi?
To delete a UFW rule, you can use sudo ufw delete followed by the rule specification.
10. How to run a firewall on Raspberry Pi?
To run a firewall on Raspberry Pi, you can install and configure firewall software like UFW or iptables. UFW provides an easier-to-use interface.
11. Can you use a Raspberry Pi as a security system?
Yes, you can set up a Raspberry Pi as a security system by installing security software, cameras, and sensors. It can monitor and alert you about events within its environment.
12. How to know if the firewall is on?
You can check if the firewall (UFW) is on by using the command: sudo ufw status.
13. How to turn Raspberry Pi into a VPN server?
You can turn a Raspberry Pi into a VPN server by installing VPN server software like OpenVPN or WireGuard and configuring it to handle VPN connections.
14. Is Raspberry Pi good for VPN?
Yes, Raspberry Pi is suitable for running a VPN server. However, its performance might vary based on the VPN protocol and the number of simultaneous connections.
15. Is UFW an application firewall?
UFW is primarily a network firewall that manages iptables rules. It controls traffic based on ports and IP addresses, rather than focusing on specific applications.
16. What does UFW limit do?
UFW limit is used to implement connection rate limiting on a specific port. It allows a limited number of new connections within a specified time window to prevent abuse.
17. Why do hackers use Raspberry Pi?
Hackers might use Raspberry Pi for various purposes, including testing security vulnerabilities, running network tools, or even building malicious devices. However, Raspberry Pi is a versatile tool with legitimate and educational use cases as well.
18. Does Raspberry Pi support WPA2?
Yes, Raspberry Pi supports WPA2 (Wi-Fi Protected Access 2), a commonly used security protocol for securing wireless networks. You can configure Wi-Fi connections on a Raspberry Pi using WPA2 encryption.
19. How do I install UFW on my Raspberry Pi?
To install UFW on your Raspberry Pi, open a terminal and run the command sudo apt-get install ufw. This command will download and install UFW on your system.
20. Can I enable UFW to start automatically when my Raspberry Pi boots up?
Yes, you can enable UFW to start automatically by using the command sudo ufw enable. This ensures that the firewall is active every time your Raspberry Pi is powered on or restarted.
21. What are default policies, and how do I set them?
Default policies define what happens to network traffic that doesn’t match any explicitly defined rules. It’s recommended to set the default policies to deny incoming traffic and allow outgoing traffic. You can achieve this by running the commands sudo ufw default deny incoming and sudo ufw default allow outgoing.
22. How do I create rules to allow or deny specific types of traffic?
To create rules, you can use commands like sudo ufw allow to allow traffic on a specific port or sudo ufw deny to deny traffic on a specific port. For example, sudo ufw allow ssh will allow SSH access, and sudo ufw deny 80/tcp will deny traffic on port 80 [7].
23. Can I log firewall events using UFW?
Yes, you can enable logging for UFW to track denied connections and other firewall-related events. Use the command sudo ufw logging on to enable logging. The logs are stored in the file /var/log/ufw.log.
24. What are application profiles, and how do I use them with UFW?
UFW includes predefined application profiles that simplify the process of allowing specific services. You can list available profiles using sudo ufw app list and then allow a specific profile, such as ‘OpenSSH’, using sudo ufw allow OpenSSH.
25. How can I limit the rate of incoming connections to prevent abuse?
To limit the rate of incoming connections from a specific IP address, you can use the command sudo ufw limit from to any port . This helps prevent abuse and brute force attacks [8].
26. Does UFW support IPv6 on the Raspberry Pi?
Yes, UFW supports IPv6. You can configure UFW to manage IPv6 traffic by enabling IPv6 support in the UFW configuration file. Open the file using sudo nano /etc/default/ufw, change IPV6=no to IPV6=yes, and save the changes.
27. Is it possible to review the active UFW rules and status?
Yes, you can check the status of UFW and view a list of active rules by using the command sudo ufw status verbose. This provides a comprehensive overview of the firewall’s current configuration and its impact on network traffic.
Useful Video: Secure your Raspberry Pi with a Firewall! (UFW Tutorial)
References
- https://pimylifeup.com/raspberry-pi-ufw/
- https://linuxhint.com/set-up-ufw-firewall-raspberry-pi/
- https://www.wundertech.net/raspberry-pi-firewall-configuration-with-ufw/
- https://raspberrytips.com/configure-firewall-raspberry-pi/
- https://www.addictedtotech.net/how-to-install-and-configure-ufw-firewall-on-a-raspberry-pi-4/
- https://linuxiac.com/raspberry-pi-firewall/
- https://raspians.com/raspberry-pi-firewall/
- https://adamtheautomator.com/raspberry-pi-firewall/


Leave a Reply